Imagine your computer or business network as a castle. This castle has valuable assets inside, like your personal data or sensitive company information, which need to be protected. The NIST CSF is like a guidebook for building and maintaining the castle's defenses against invaders, which in this case are cyber threats.
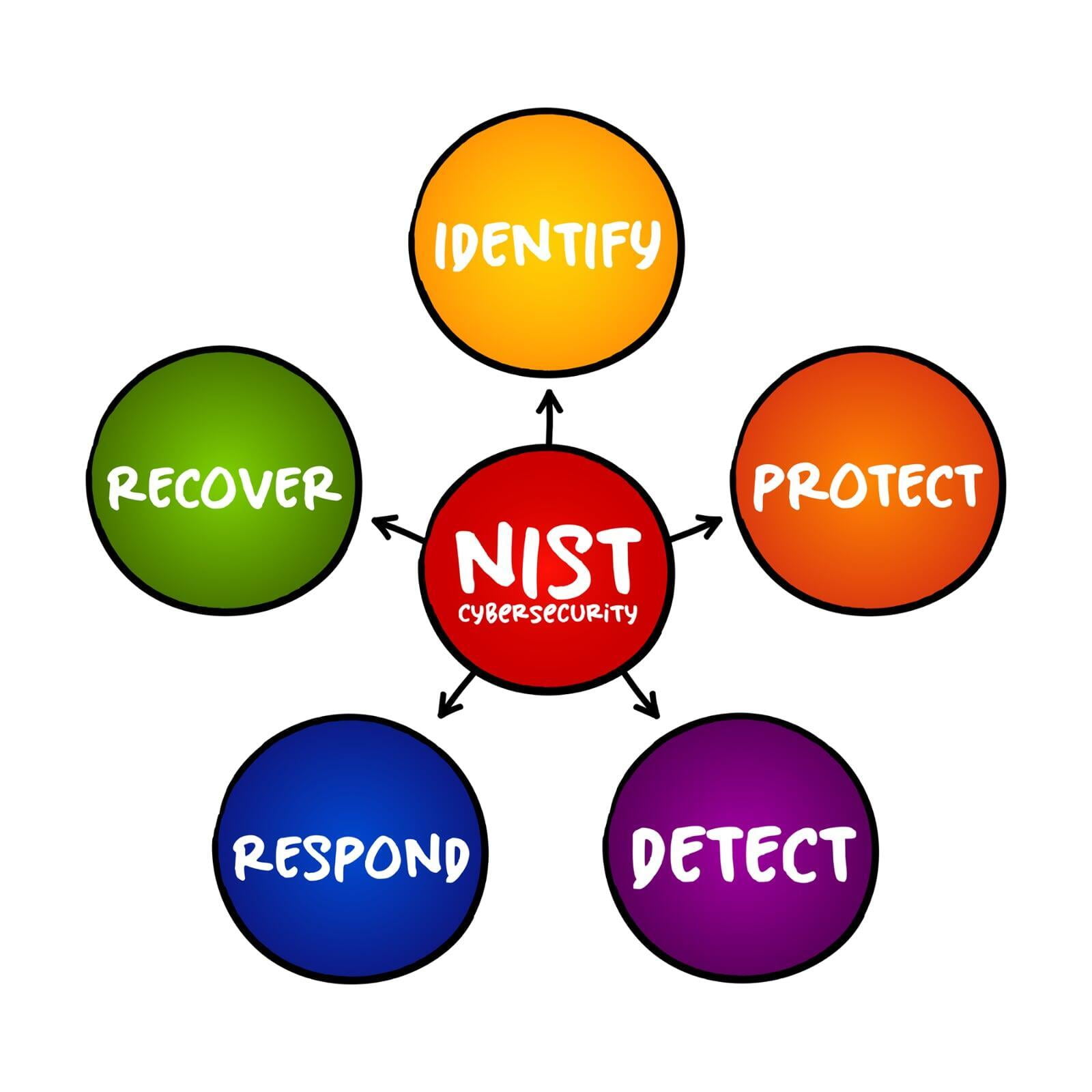
The guidebook is divided into five main sections, each representing a different part of your cybersecurity strategy:
Identify- Before you can protect anything, you need to know what you're protecting. This includes knowing the layout of the castle, what's valuable inside it, and who has access to it.
Protect - This is where you build up your defenses. You put in place walls, moats, and drawbridges (which could represent things like firewalls, encryption, and user authentication) to keep the bad guys out.
Detect - You need to know when an invader is trying to get in or if they have already gotten in. This is like having sentries or alarm systems (like intrusion detection systems) in place that can alert you to suspicious activity.
Respond - If an invader does manage to breach your defenses, you need to have a plan in place for dealing with them. This can include isolating affected areas, repairing damage, and pursuing the invader.
Recover - After an attack, you need to restore any damage done. This is where you repair the castle walls, replace anything that was stolen, and learn from what happened to improve your defenses in the future.
The NIST CSF isn't mandatory, but NIST is widely respected and used by organizations because it offers a clear, structured approach to cybersecurity. NIST also provides a common language that can be used across different teams and organizations, making it easier to communicate about cybersecurity issues.